Usage
Install
-
Prerequisite:
~/.aws/credentialsneeds to be configured, e.g. by installing the AWS CLI and runningaws configure - For details and troubleshooting please refer to the Wiki.
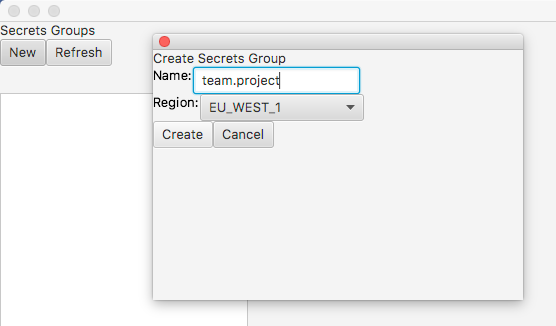
Create a Secrets Group
A Secrets Group is a collection of secrets that are managed together. When you create a Secrets Group, Strongbox will allocate a DynamoDB table, a KMS Encryption Key, and two IAM Policies: one for read-only access to the Secrets Group, and one for admin access.
The KMS key will be used for envelope encryption using the AWS Encryption SDK. DynamoDB will store all the data, most of which is encrypted. The IAM policies will limit the access to the DynamoDB table and the KMS key as appropriate for the respective access level.
You can omit --region <region> if you have specified a region in ~/.aws/config. You can specify an AWS profile using --profile <profile>, otherwise the default profile will be used.
Assume role and MFA config can also be specified in ~/.aws/config.
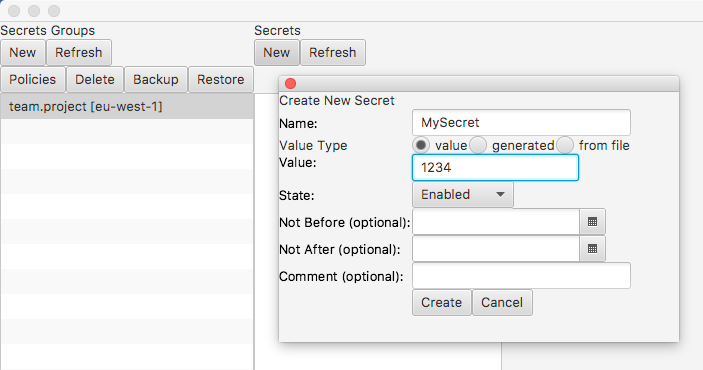
Create a Secret
You can create a secret from an existing value, from a file or by generating one using KMS. When you create a secret it will be encrypted using the KMS Encryption SDK and stored in DynamoDB.
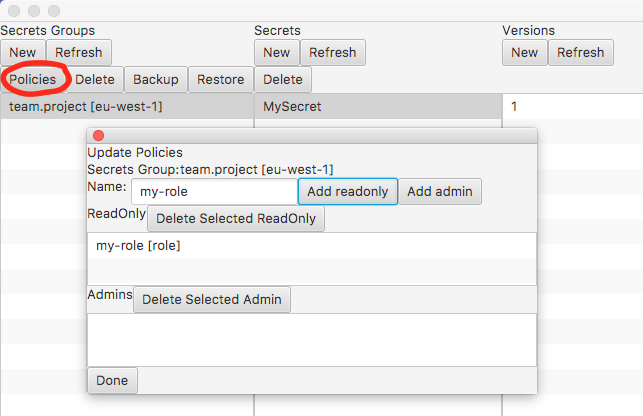
Grant Read-only Access to a Secrets Group
Read-only access is provided on a per Secrets Group basis. To help avoid misconfiguration Strongbox generates a suitable read-only policy for you. Access is granted by attaching to this policy, either using one of AWS' methods of doing so, or by using Strongbox as shown below.
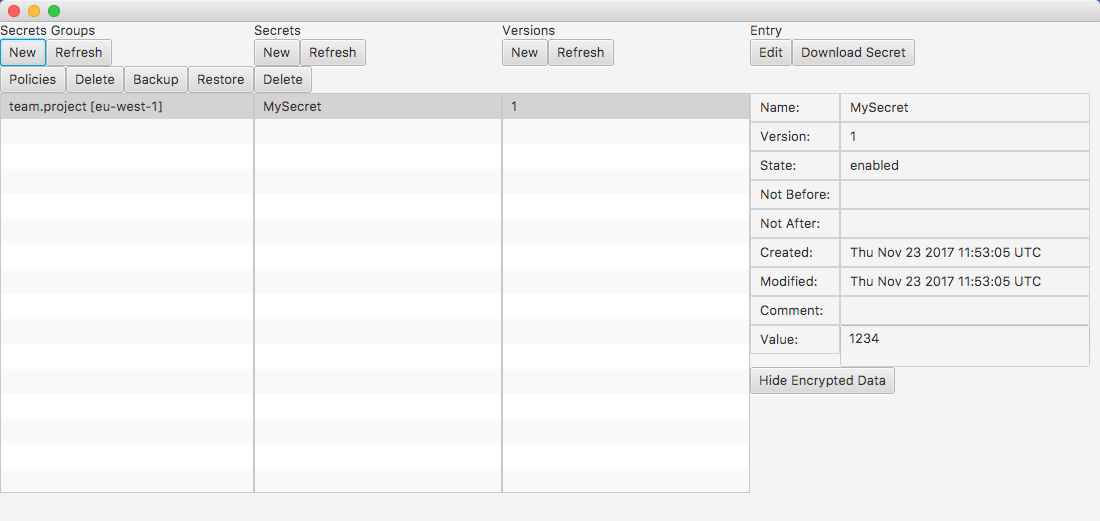
Fetch a Secret
Secrets are read from DynamoDB and then decrypted using the AWS Encryption SDK. In addition to the examples below there are also integrations with Spring Boot and Archaius.